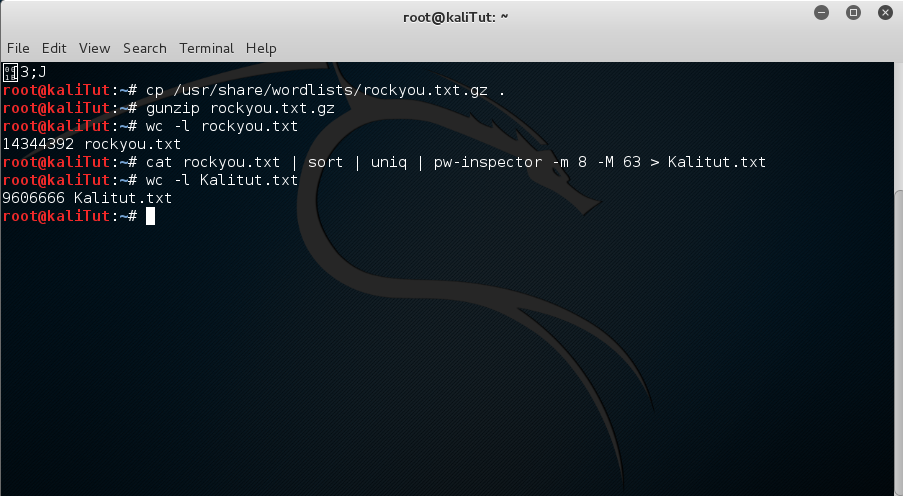
Rockyoutxt Password List Download
Kali linux is a distribution designed for penetration testing and computer forensics, both which involve password cracking. So you are right in thinking that word lists are involved in password cracking, however it's not brute force.
Nov 20, 2018 A wordlist or a password dictionary is a collection of passwords stored in plain text. It's basically a text file with a bunch of passwords in it. Most of the wordlists you can download online including the ones I share with you here are a collection of uncommon and common passwords that were once used (and probably still is) by real people.
Brute force attacks try every combination of characters in order to find a password, while word lists are used in dictionary based attacks. Many people base their password on dictionary words, and word lists are used to supply the material for dictionary attacks.
The reason you want to use dictionary attacks is that they are much faster than brute force attacks. If you have many passwords and you only want to crack one or two then this method can yield quick results, especially if the password hashes are from places where strong passwords are not enforced.
Typical tools for password cracking (John the Ripper, ophtcrack, hashcat, etc) can do several types of attacks including: • Standard brute force: all combinations are tried until something matches. You tpyically use a character set common on the keyboards of the language used to type the passwords, or you can used a reduced set like alphanumneric plus a few symbols. 
The size of the character set makes a big difference in how long it takes to brute force a password. Password length also makes a big difference.
This can take a very long time depending on many factors • Standard dictionary: straight dictionary words are used. It's mostly used to find really poor passwords, like password, password123, system, welcome, 123456, etc. • Dictionary attack with rules: in this type dictionary words are used as the basis for cracks, rules are used to modify these, for instance capitalizing the first letter, adding a number to the end, or replacing letters with numbers or symbols Rules attacks are likely the best bang for the buck if all you have are standard computing resources, although if you have GPUs available brute-force attacks can be made viable as long as the passwords aren't too long. It depends on the password length, hashing/salting used, and how much computing power you have at your disposal.
In addition to what's already mentioned here, the wordlists are used in conjunction with some of the web app tools and things such as sqlmap. If you're looking for places to use them, download some of the 'boot to root' VMs like Kioptrix and De-ICE and have a go at brute-ing some passwords. As for specific lists for specific types of hacks - not really. David hamilton photo girl seated chair. Unless you're doing something targeted against a person you know some facts about (in which case you'll use something like CUPP - Common User Passwords Profiler - to generate a custom wordlist for that particular target).
Cracking windows passwords is no more difficult than any other set of passwords that need to be cracked via brute force/rainbow table lookup -- it's all about getting your hands on the right files to begin with. Note that Vista and Windows 7 are the same in terms of how the passwords are stored. XP is different. You'll need to appropriate hash tables when cracking using Ophcrack-- you can't use XP hashes to crack Vista/7 and vice versa. I actually have a fairly legit reason for this, other than pure curiosity: the professors and lecturers who have Win 7 at this Uni aren't given administrator access, so that they need to make an appointment with IT staff everytime they want to install or upgrade something. In my opinion, that's taking things way, way too far, especially in light of OSX user and Linux users don't face the same restrictions (I requested my computer to be delivered blank, so not even the IT staff can gain access without physically accessing my hdd).